Key Takeaways
1. The Art of Offensive Forensics: Turning the Tables
The network is and always will be the sexiest arena for a hacker.
Reversing the Script. Offensive forensics involves using forensic techniques not for defense, but for attack. It's about understanding how forensic tools and investigators work to better evade detection and maintain access. This approach allows attackers to anticipate responses and tailor their actions accordingly.
Understanding the Enemy. By studying forensic methodologies, incident response procedures, and common security tools, attackers can identify vulnerabilities in the investigative process. This knowledge can be used to create more effective and stealthy attacks. For example:
- Knowing which artifacts are commonly analyzed can help attackers avoid leaving those traces.
- Understanding how memory forensics works can help attackers craft shellcode that avoids detection.
Proactive Evasion. Offensive forensics is not just about reacting to investigations, but about proactively shaping the digital landscape to make investigations more difficult. This might involve:
- Planting false evidence to mislead investigators
- Tampering with logs to obscure activity
- Using encryption to protect sensitive data
2. Keylogging: A Classic Technique for Modern Threats
Countless times during penetration tests, we (the authors) have needed to whip up a TCP client to test for services, send garbage data, fuzz, or perform any number of other tasks.
Capturing Sensitive Information. Keylogging remains a highly effective method for capturing credentials, conversations, and other sensitive data. By recording keystrokes, attackers can gain access to accounts, systems, and networks.
PyWinHook for Windows Keylogging:
- Leverages the native Windows function SetWindowsHookEx to trap keyboard events.
- Provides information about the active window and process associated with each keystroke.
- Allows for the capture of both ASCII characters and special keys.
Beyond Basic Keystrokes. Modern keyloggers can also capture clipboard data, providing access to passwords, credit card numbers, and other sensitive information that users copy and paste. This expands the scope of potential data breaches.
3. Screenshots: Capturing Visual Intelligence
Programmers have a number of third-party tools to create networked servers and clients in Python, but the core module for all of those tools is socket.
Visual Confirmation. Screenshots provide visual confirmation of user activity, capturing images, video frames, and other sensitive data that might not be accessible through other means. This can be particularly useful for gathering evidence of specific actions or behaviors.
PyWin32 for Screenshot Capture:
- Uses the Windows Graphics Device Interface (GDI) to capture the entire screen.
- Provides a way to grab images, video frames, or other sensitive data.
- Can be used to monitor user activity and gather intelligence.
Beyond Simple Screenshots. Advanced screenshot techniques can include:
- Capturing screenshots at regular intervals to create a timeline of user activity.
- Triggering screenshots based on specific events, such as the opening of a particular application.
- Using optical character recognition (OCR) to extract text from screenshots.
4. Shellcode Execution: Remote Code Injection
The network is and always will be the sexiest arena for a hacker.
Direct Code Execution. Shellcode execution allows attackers to inject and run arbitrary code on a target system without touching the filesystem. This can be used to establish a reverse shell, deploy additional malware, or perform other malicious activities.
ctypes for Shellcode Execution:
- Uses the ctypes module to allocate memory, copy shellcode into memory, and create a function pointer to the shellcode.
- Allows for the execution of raw shellcode without writing it to disk.
- Can be used to bypass security measures that rely on file-based scanning.
Beyond Basic Shellcode. Advanced shellcode techniques can include:
- Using position-independent code (PIC) to ensure that shellcode can run at any memory address.
- Encrypting shellcode to evade detection.
- Using multi-stage shellcode to download and execute larger payloads.
5. Sandbox Detection: Evading Automated Analysis
You might use one for forwarding traffic to bounce from host to host, or when assessing network-based software.
Evading Automated Defenses. Sandbox detection involves identifying and avoiding automated analysis environments used by antivirus software and security researchers. By detecting sandbox environments, attackers can prevent their malware from being analyzed and detected.
Techniques for Sandbox Detection:
- Monitoring user input: Checking for keyboard and mouse activity.
- Detecting virtual machine artifacts: Looking for specific files, registry keys, or processes associated with virtual machines.
- Analyzing system uptime: Comparing the system's uptime to the last user input.
Beyond Basic Detection. Advanced sandbox detection techniques can include:
- Using timing-based attacks to detect virtual machine environments.
- Checking for the presence of specific security tools or processes.
- Analyzing the system's hardware configuration.
6. Encryption: Securing Exfiltrated Data
On more than one occasion, I’ve run into servers that don’t have netcat installed but do have Python.
Protecting Sensitive Information. Encryption is essential for protecting sensitive data during exfiltration. By encrypting data before it leaves the target system, attackers can prevent unauthorized access to the information even if it is intercepted.
PyCryptodomeX for Encryption:
- Provides a variety of encryption algorithms, including AES and RSA.
- Allows for the creation of hybrid encryption systems that combine the speed of symmetric encryption with the security of asymmetric encryption.
- Can be used to encrypt files, network traffic, or other sensitive data.
Beyond Basic Encryption. Advanced encryption techniques can include:
- Using steganography to hide encrypted data within images or other files.
- Using multiple layers of encryption to increase security.
- Using ephemeral keys to ensure that data cannot be decrypted even if the attacker's keys are compromised.
7. Exfiltration Methods: Blending in to Get Out
The network is and always will be the sexiest arena for a hacker.
Stealth and Evasion. Choosing the right exfiltration method is crucial for avoiding detection. Attackers must consider the target network's security posture and choose a method that blends in with normal traffic.
Common Exfiltration Methods:
- Email: Sending encrypted data as attachments or within the body of emails.
- File transfer: Using FTP or other file transfer protocols to upload encrypted data to a remote server.
- Web server: Posting encrypted data to a web server using HTTP or HTTPS.
Beyond Basic Exfiltration. Advanced exfiltration techniques can include:
- Using steganography to hide encrypted data within images or other files.
- Using covert channels to transmit data over seemingly innocuous protocols.
- Using distributed exfiltration to spread data across multiple destinations.
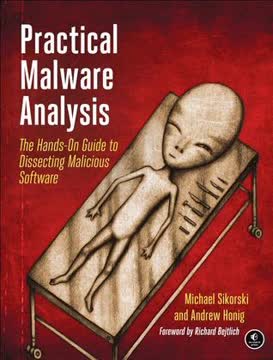
Review Summary
Black Hat Python receives mixed reviews. Many praise its practical examples and insights into using Python for hacking and penetration testing. Readers appreciate the hands-on approach and clear explanations of complex concepts. However, some criticize its use of outdated Python versions and reliance on Windows-specific content. The book is recommended for those with prior Python experience but may be challenging for beginners. Overall, it's considered a valuable resource for aspiring ethical hackers and security professionals, despite some limitations.
People Also Read




FAQ
What's "Black Hat Python: Python Programming for Hackers and Pentesters" about?
- Focus on offensive security: The book delves into using Python for creating hacking tools, focusing on offensive security techniques.
- Practical applications: It covers writing network sniffers, manipulating packets, and creating stealthy trojans, among other tasks.
- Comprehensive guide: The book provides a step-by-step approach to building tools that can be used in real-world penetration testing scenarios.
- Author's expertise: Written by Justin Seitz, known for his work in security analysis, the book leverages his extensive experience in the field.
Why should I read "Black Hat Python: Python Programming for Hackers and Pentesters"?
- Learn from an expert: Justin Seitz is a seasoned security consultant, offering insights from his experience with Fortune 500 companies and law enforcement.
- Hands-on approach: The book is practical, with exercises and examples that help readers apply what they learn immediately.
- Expand your toolkit: It teaches how to create custom tools, which is invaluable for penetration testers and security professionals.
- Stay updated: The book covers the latest techniques and tools, ensuring readers are equipped with current knowledge in cybersecurity.
What are the key takeaways of "Black Hat Python: Python Programming for Hackers and Pentesters"?
- Python's versatility: Python is highlighted as a powerful language for security analysis and tool creation.
- Custom tool development: Readers learn to write their own exploits and extend existing tools like Burp Suite.
- Network and web hacking: The book covers essential skills for network sniffing, web application attacks, and privilege escalation.
- Ethical hacking mindset: It emphasizes the importance of understanding both offensive and defensive security measures.
What are the best quotes from "Black Hat Python" and what do they mean?
- "The difference between script kiddies and professionals is the difference between merely using other people’s tools and writing your own." This quote underscores the importance of creating custom tools to truly understand and master hacking techniques.
- "When it comes to offensive security, your ability to create powerful tools on the fly is indispensable." It highlights the necessity of being adaptable and resourceful in cybersecurity.
- "Learn how to extend the hacks and how to write your own exploits." This encourages readers to go beyond using existing tools and develop their own solutions.
How does "Black Hat Python" teach network sniffing and packet manipulation?
- Raw sockets: The book explains how to use raw sockets to access low-level networking information, such as IP and ICMP headers.
- Packet decoding: It covers decoding IP and ICMP packets to extract useful information like protocol types and IP addresses.
- Practical examples: Readers are guided through creating a UDP host discovery tool and a simple sniffer to capture network traffic.
- Cross-platform techniques: The book provides solutions for both Windows and Linux environments, ensuring broad applicability.
What is the role of Scapy in "Black Hat Python"?
- Powerful library: Scapy is introduced as a versatile tool for packet manipulation and network analysis.
- Sniffing and ARP poisoning: The book demonstrates using Scapy to sniff traffic and perform ARP cache poisoning attacks.
- Image extraction: It includes a project on extracting images from HTTP traffic and performing facial detection using OpenCV.
- Efficiency and flexibility: Scapy simplifies tasks that would otherwise require extensive coding, making it a valuable asset for hackers.
How does "Black Hat Python" approach web application hacking?
- Web libraries: The book covers using libraries like urllib2, requests, and lxml for interacting with web services.
- Brute-forcing techniques: It teaches how to brute-force directories, file locations, and HTML form authentication.
- WordPress example: A specific example is provided for brute-forcing WordPress logins, highlighting common vulnerabilities.
- Custom tooling: Readers learn to create tools for mapping web app installations and discovering hidden files and directories.
What is the significance of GitHub in "Black Hat Python"?
- Command and control: GitHub is used as a platform for storing configuration information and exfiltrating data from victim systems.
- Module management: The book explains how to host trojan modules on GitHub and dynamically import them into a trojan.
- Encrypted communication: Using GitHub ensures encrypted communication over SSL, making it a stealthy option for attackers.
- Practical implementation: Readers are guided through setting up a GitHub account and creating a trojan framework that leverages the platform.
How does "Black Hat Python" address privilege escalation on Windows?
- Process monitoring: The book teaches how to use WMI to monitor process creation and identify high-privilege processes.
- File monitoring: It covers using ReadDirectoryChangesW to track file changes and inject code into high-privilege processes.
- Privilege analysis: Readers learn to analyze Windows token privileges to identify potential escalation opportunities.
- Real-world examples: The book provides practical examples of exploiting insecure file handling and scheduled tasks.
What are the offensive forensics techniques discussed in "Black Hat Python"?
- Volatility framework: The book introduces Volatility for memory forensics and analyzing VM snapshots.
- User and process recon: It covers using Volatility to gather information about user behavior and running processes.
- Custom plug-ins: Readers learn to write their own Volatility plug-ins to check for vulnerabilities like ASLR protection.
- Practical applications: The techniques are applied to real-world scenarios, such as analyzing VM snapshots for vulnerabilities.
How does "Black Hat Python" teach exfiltration techniques?
- Encryption methods: The book covers using PyCryptoDomeX for encrypting and decrypting files before exfiltration.
- Multiple channels: It teaches exfiltration via email, file transfers, and web server posts, with both platform-independent and Windows-specific methods.
- COM automation: Windows COM automation is used to exfiltrate data stealthily, leveraging trusted processes like Internet Explorer.
- Comprehensive approach: The book provides a range of techniques to ensure successful data exfiltration in various network environments.
Download PDF
Download EPUB
.epub digital book format is ideal for reading ebooks on phones, tablets, and e-readers.